Vaibhav Kumar
Design of Uplink ISAC Systems with Cooperative Sensing: Power Control and Receive Beamforming
Mar 18, 2026Abstract:Integrated sensing and communication (ISAC) has emerged as a key paradigm for next-generation wireless systems, which allows wireless resources to be used for data transmission and target sensing simultaneously. In this paper, multi-user collaborative target detection in the uplink ISAC system is investigated. To incorporate the target sensing functionality, the system relies on the reuse of uplink signals from the communication users. Specifically, we analyze an uplink multi-user single-input multiple-output (MU-SIMO) communication system with bistatic sensing. Using the channel statistics, we formulate the problem of joint optimal pilot and data power allocation to maximize the uplink ergodic sum rate while meeting communication and sensing quality-of-service (QoS) requirements. To address this non-convex problem, we propose an alternating optimization (AO)-based iterative framework, where the joint power allocation problem is decomposed into two sub-problems. Specifically, the pilot power allocation is optimized using a penalty dual decomposition (PDD)-based gradient ascent algorithm, while the data power allocation is solved via successive convex approximation (SCA). Once the long-term power allocation is determined, the base station (BS) estimates the instantaneous channels using a minimum mean-squared error (MMSE) estimator. Subsequently, based on the estimated instantaneous channel state information (CSI), the receive beamforming for communication users is optimized via another SCA-based method to maximize the sum rate. Meanwhile, the optimal receive beamforming for the target is obtained in closed-form through eigenvalue decomposition (EVD).
Beyond the Limits of Rigid Arrays: Flexible Intelligent Metasurfaces for Next-Generation Wireless Networks
Mar 12, 2026Abstract:Following recent advances in flexible electronics and programmable metasurfaces, flexible intelligent metasurfaces (FIMs) have emerged as a promising enabling technology for next-generation wireless networks. A FIM is a morphable electromagnetic surface capable of dynamically adjusting its physical geometry to influence the radiation and propagation of electromagnetic waves. Unlike conventional rigid arrays, FIMs introduce an additional spatial degree of design freedom enabled by mechanical flexibility, which can enhance beamforming, spatial focusing, and adaptation to dynamic wireless environments. This added capability enables wireless systems to shape the propagation environment not only through electromagnetic tuning but also through controllable geometric reconfiguration. This article explores the potential of FIMs for next-generation wireless networks. We first introduce the main hardware architectures of FIMs and explain how they can be integrated into wireless communication systems. We then present representative application scenarios, highlighting the advantages of FIMs for future wireless networks and comparing them with other emerging flexible wireless technologies. To illustrate their potential impact, we present case studies comparing FIM-enabled architectures with conventional rigid-array systems, demonstrating the performance gains enabled by surface flexibility for both communication and sensing applications. Finally, we discuss key opportunities, practical challenges, and open research directions that must be addressed to fully realize the potential of FIM technology in future wireless communication systems.
Exploiting Structural Flexibility in SIM-Enabled Communications: From Adaptive Inter-Layer Spacing to Fully Morphable Layers
Feb 12, 2026Abstract:Stacked intelligent metasurfaces (SIMs) have recently emerged as a promising metasurface-based physical-layer paradigm for wireless communications, enabling wave-domain signal processing through multiple cascaded metasurface layers. However, conventional SIM designs rely on rigid planar layers with fixed interlayer spacing, which constrain the propagation geometry and can lead to performance saturation as the number of layers increases. This paper investigates the potential of introducing structural flexibility into SIM-enabled communication systems. Specifically, we consider two flexible SIM architectures: distance-adaptive SIM (DSIM), where interlayer distances are optimized, and stacked flexible intelligent metasurface (SFIM), where each metasurface layer is fully morphable. We jointly design the meta-atom positions and responses together with the transmit beamformer to maximize the system sum rate under per-user rate, quantization, morphing, and interlayer distance constraints. An alternating optimization framework combining gradient projection, penalty-based method, and successive convex approximation is developed to address the resulting non-convex problems. Perturbation analysis reveals that the flexibility gains of both DSIM and SFIM scale approximately linearly with the morphing range, with SFIM exhibiting a faster growth rate. Simulation results demonstrate that flexible SIM designs mitigate performance saturation with increasing layers and achieve significant transmit power savings compared to rigid SIMs.
Flexible Intelligent Metasurface for Downlink Communications under Statistical CSI
Dec 28, 2025Abstract:Flexible intelligent metasurface (FIM) is a recently developed, groundbreaking hardware technology with promising potential for 6G wireless systems. Unlike conventional rigid antenna array (RAA)-based transmitters, FIM-assisted transmitters can dynamically alter their physical surface through morphing, offering new degrees of freedom to enhance system performance. In this letter, we depart from prior works that rely on instantaneous channel state information (CSI) and instead address the problem of average sum spectral efficiency maximization under statistical CSI in a FIM-assisted downlink multiuser multiple-input single-output setting. To this end, we first derive the spatial correlation matrix for the FIM-aided transmitter and then propose an iterative FIM optimization algorithm based on the gradient projection method. Simulation results show that with statistical CSI, the FIM-aided system provides a significant performance gain over its RAA-based counterpart in scenarios with strong spatial channel correlation, whereas the gain diminishes when the channels are weakly correlated.
Hiding in Plain Sight: RIS-Aided Target Obfuscation in ISAC
Mar 07, 2025Abstract:Integrated sensing and communication (ISAC) has been identified as a promising technology for the sixth generation (6G) of communication networks. Target privacy in ISAC is essential to ensure that only legitimate sensors can detect the target while keeping it hidden from malicious ones. In this paper, we consider a downlink reconfigurable intelligent surface (RIS)-assisted ISAC system capable of protecting a sensing region against an adversarial detector. The RIS consists of both reflecting and sensing elements, adaptively changing the element assignment based on system needs. To achieve this, we minimize the maximum sensing signal-to-interference-plus-noise-ratio (SINR) at the adversarial detector within sample points in the sensing region, by optimizing the transmit beamformer at the base station, the RIS phase shift matrix, the received beamformer at the RIS, and the division between reflecting and absorptive elements at the RIS, where the latter function as sensing elements. At the same time, the system is designed to maintain a minimum sensing SINR at each monitored location, as well as minimum communication SINR for each user. To solve this challenging optimization problem, we develop an alternating optimization approach combined with a successive convex approximation based method tailored for each subproblem. Our results show that the proposed approach achieves a 25 dB reduction in the maximum sensing SINR at the adversarial detector compared to scenarios without sensing area protection. Also, the optimal RIS element assignment can further improve sensing protection by 3 dB over RISs with fixed element configuration.
Beamforming Design for Secure RIS-Enabled ISAC: Passive RIS vs. Active RIS
Jan 31, 2025Abstract:The forthcoming sixth-generation (6G) communications standard is anticipated to provide integrated sensing and communication (ISAC) as a fundamental service. These ISAC systems present unique security challenges because of the exposure of information-bearing signals to sensing targets, enabling them to potentially eavesdrop on sensitive communication information with the assistance of sophisticated receivers. Recently, reconfigurable intelligent surfaces (RISs) have shown promising results in enhancing the physical layer security of various wireless communication systems, including ISAC. However, the performance of conventional passive RIS (pRIS)-enabled systems are often limited due to multiplicative fading, which can be alleviated using active RIS (aIRS). In this paper, we consider the problem of beampattern gain maximization in a secure pRIS/aRIS-enabled ISAC system, subject to signal-to-interference-plus-noise ratio constraints at communication receivers, and information leakage constraints at an eavesdropping target. For the challenging non-convex problem of joint beamforming design at the base station and the pRIS/aRIS, we propose a novel successive convex approximation (SCA)-based method. Unlike the conventional alternating optimization (AO)-based methods, in the proposed SCA-based approach, all of the optimization variables are updated simultaneously in each iteration. The proposed method shows significant performance superiority for pRIS-aided ISAC system compared to a benchmark scheme using penalty-based AO method. Moreover, our simulation results also confirm that aRIS-aided system has a notably higher beampattern gain at the target compared to that offered by the pRIS-aided system for the same power budget. We also present a detailed complexity analysis and proof of convergence for the proposed SCA-based method.
PAFFA: Premeditated Actions For Fast Agents
Dec 10, 2024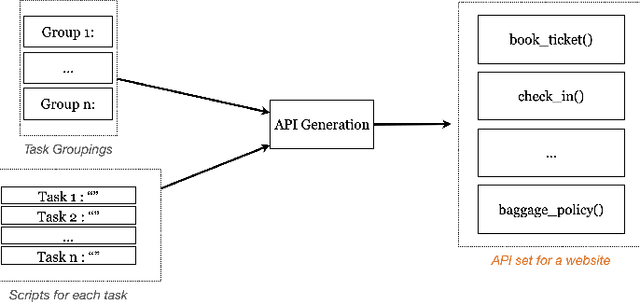
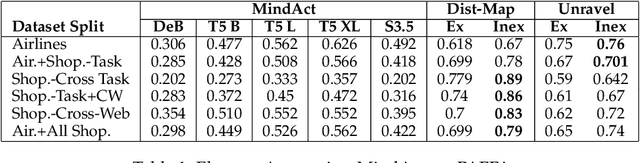
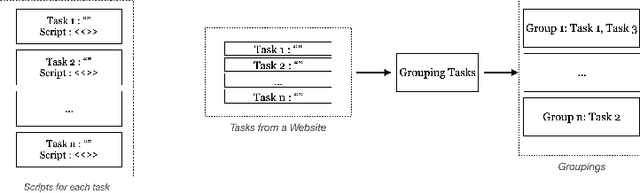
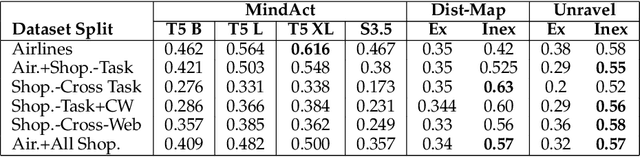
Abstract:Modern AI assistants have made significant progress in natural language understanding and API/tool integration, with emerging efforts to incorporate diverse interfaces (such as Web interfaces) for enhanced scalability and functionality. However, current approaches that heavily rely on repeated LLM-driven HTML parsing are computationally expensive and error-prone, particularly when handling dynamic web interfaces and multi-step tasks. To overcome these challenges, we introduce PAFFA (Premeditated Actions For Fast Agents), a framework designed to enhance web interaction capabilities through an Action API Library of reusable, verified browser interaction functions. By pre-computing interaction patterns and employing two core methodologies - "Dist-Map" for task-agnostic element distillation and "Unravel" for incremental page-wise exploration - PAFFA reduces inference calls by 87% while maintaining robust performance even as website structures evolve. This framework accelerates multi-page task execution and offers a scalable solution to advance autonomous web agent research.
Optimal Beamforming Design for ISAC with Sensor-Aided Active RIS
Oct 16, 2024Abstract:Active reconfigurable intelligent surfaces (RISs) can improve the performance of integrated sensing and communication (ISAC), and therefore enable simultaneous data transmission and target sensing. However, when the line-of-sight (LoS) link between the base station and the sensing target is blocked, the sensing signals suffer from severe path loss, resulting in an inferior sensing performance. To address this issue, this paper employs a sensor-aided active RIS to enhance ISAC system performance. The goal is to maximize the signal-to-noise ratio of the echo signal from the target at the sensor-array while meeting constraints on communication signal quality, power budgets, and RIS amplification limits. The optimization problem is challenging due to its non-convex nature and the coupling between the optimization variables. We propose a closed-form solution for receive beamforming, and a successive convex approximation based iterative method for transmit and reflection beamforming design. Simulation results demonstrate the advantage of the proposed sensor-aided active RIS-assisted system model over its non-sensor-aided counterpart.
Multi-Functional RIS for a Multi-Functional System: Integrating Sensing, Communication, and Wireless Power Transfer
Oct 11, 2024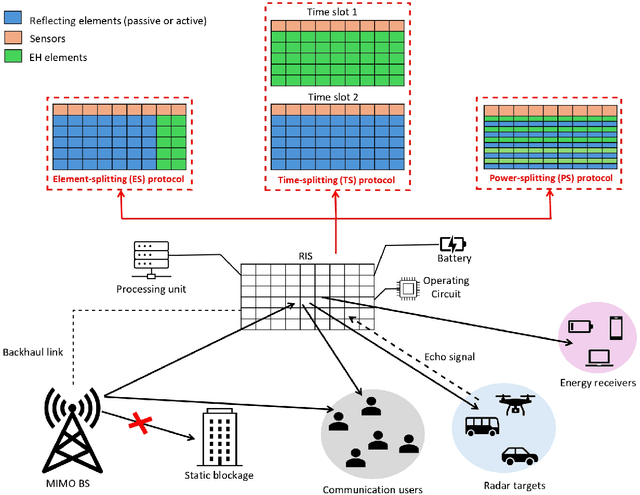
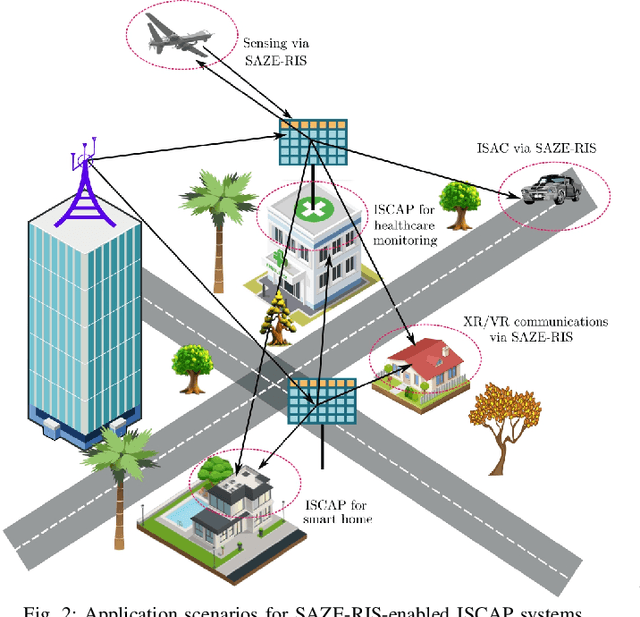
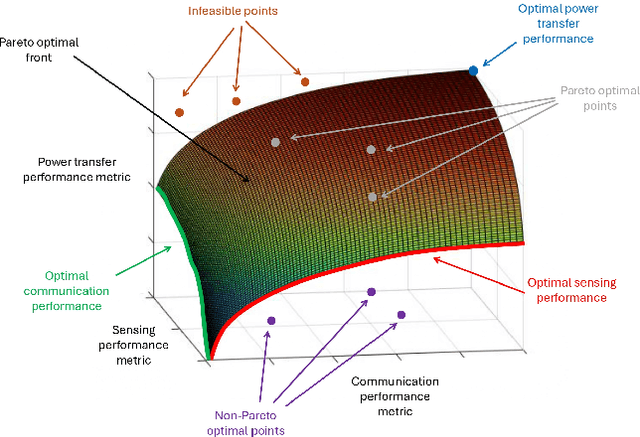
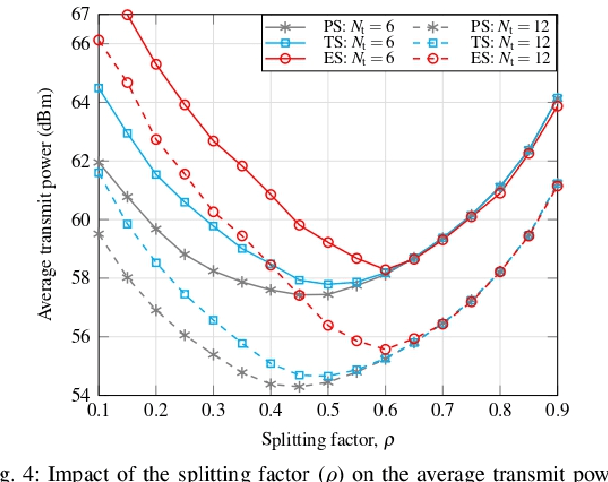
Abstract:Communication networks are evolving from solely emphasizing communication to facilitating multiple functionalities. In this regard, integrated sensing, communication, and powering (ISCAP) provides an efficient way of enabling data transmission, radar sensing, and wireless power transfer simultaneously. Such a multi-functional network requires a multi-functional architectural solution. Toward this end, sensor-aided zero-energy reconfigurable intelligent surfaces (SAZE-RISs) offer an energy-efficient solution for ISCAP by meeting the requirements of the end users as well as supplying power for the RIS. This paper explores the use of SAZE-RIS within the ISCAP framework. First, we present the general system architecture, operational protocols, and main application scenarios for employing SAZE-RIS in ISCAP. Next, we discuss methods for managing the conflicting requirements of communication, sensing, and powering within ISCAP and the role of SAZE-RIS in this process. We then provide a detailed case study complete with simulation results, offering valuable insights into the design choices and tradeoffs that come into play when adopting this technology. Furthermore, we discuss the related challenges and open research avenues, highlighting areas that require further exploration to fully realize the potential of SAZE-RIS within this ISCAP framework.
Breaking Down the Defenses: A Comparative Survey of Attacks on Large Language Models
Mar 03, 2024

Abstract:Large Language Models (LLMs) have become a cornerstone in the field of Natural Language Processing (NLP), offering transformative capabilities in understanding and generating human-like text. However, with their rising prominence, the security and vulnerability aspects of these models have garnered significant attention. This paper presents a comprehensive survey of the various forms of attacks targeting LLMs, discussing the nature and mechanisms of these attacks, their potential impacts, and current defense strategies. We delve into topics such as adversarial attacks that aim to manipulate model outputs, data poisoning that affects model training, and privacy concerns related to training data exploitation. The paper also explores the effectiveness of different attack methodologies, the resilience of LLMs against these attacks, and the implications for model integrity and user trust. By examining the latest research, we provide insights into the current landscape of LLM vulnerabilities and defense mechanisms. Our objective is to offer a nuanced understanding of LLM attacks, foster awareness within the AI community, and inspire robust solutions to mitigate these risks in future developments.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge