Savio Sciancalepore
Challenges of Radio Frequency Fingerprinting: From Data Collection to Deployment
Oct 25, 2023Abstract:Radio Frequency Fingerprinting (RFF) techniques promise to authenticate wireless devices at the physical layer based on inherent hardware imperfections introduced during manufacturing. Such RF transmitter imperfections are reflected into over-the-air signals, allowing receivers to accurately identify the RF transmitting source. Recent advances in Machine Learning, particularly in Deep Learning (DL), have improved the ability of RFF systems to extract and learn complex features that make up the device-specific fingerprint. However, integrating DL techniques with RFF and operating the system in real-world scenarios presents numerous challenges. This article identifies and analyzes these challenges while considering the three reference phases of any DL-based RFF system: (i) data collection and preprocessing, (ii) training, and finally, (iii) deployment. Our investigation points out the current open problems that prevent real deployment of RFF while discussing promising future directions, thus paving the way for further research in the area.
PAST-AI: Physical-layer Authentication of Satellite Transmitters via Deep Learning
Oct 12, 2020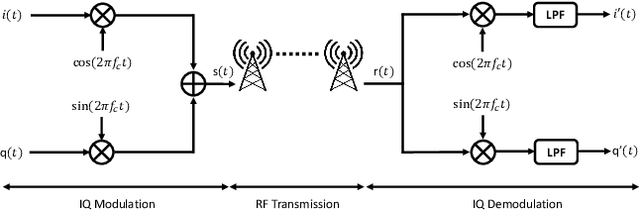

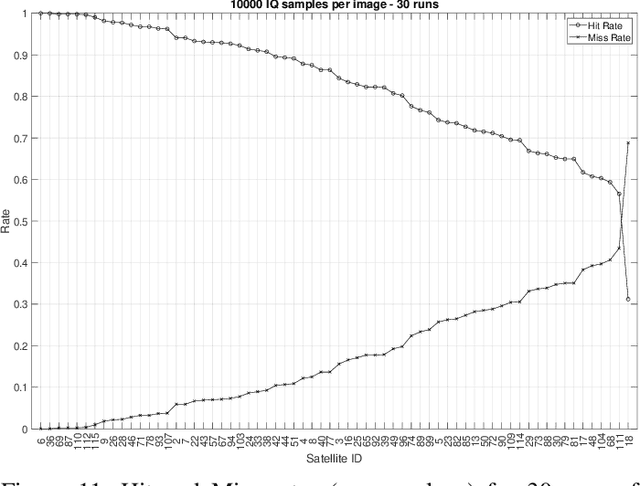
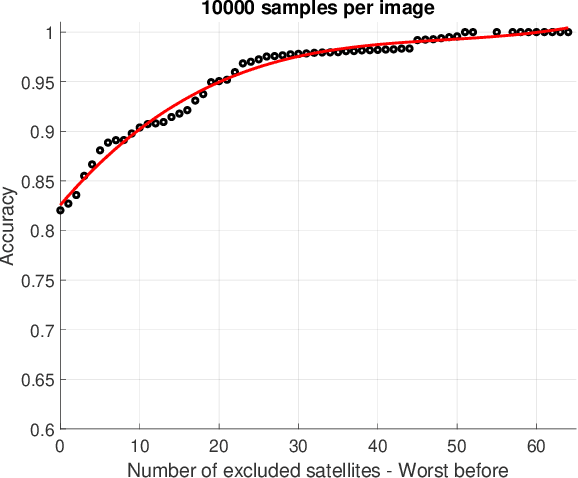
Abstract:Physical-layer security is regaining traction in the research community, due to the performance boost introduced by deep learning classification algorithms. This is particularly true for sender authentication in wireless communications via radio fingerprinting. However, previous research efforts mainly focused on terrestrial wireless devices while, to the best of our knowledge, none of the previous work took into consideration satellite transmitters. The satellite scenario is generally challenging because, among others, satellite radio transducers feature non-standard electronics (usually aged and specifically designed for harsh conditions). Moreover, the fingerprinting task is specifically difficult for Low-Earth Orbit (LEO) satellites (like the ones we focus in this paper) since they orbit at about 800Km from the Earth, at a speed of around 25,000Km/h, thus making the receiver experiencing a down-link with unique attenuation and fading characteristics. In this paper, we propose PAST-AI, a methodology tailored to authenticate LEO satellites through fingerprinting of their IQ samples, using advanced AI solutions. Our methodology is tested on real data -- more than 100M I/Q samples -- collected from an extensive measurements campaign on the IRIDIUM LEO satellites constellation, lasting 589 hours. Results are striking: we prove that Convolutional Neural Networks (CNN) and autoencoders (if properly calibrated) can be successfully adopted to authenticate the satellite transducers, with an accuracy spanning between 0.8 and 1, depending on prior assumptions. The proposed methodology, the achieved results, and the provided insights, other than being interesting on their own, when associated to the dataset that we made publicly available, will also pave the way for future research in the area.
Noise2Weight: On Detecting Payload Weight from Drones Acoustic Emissions
May 04, 2020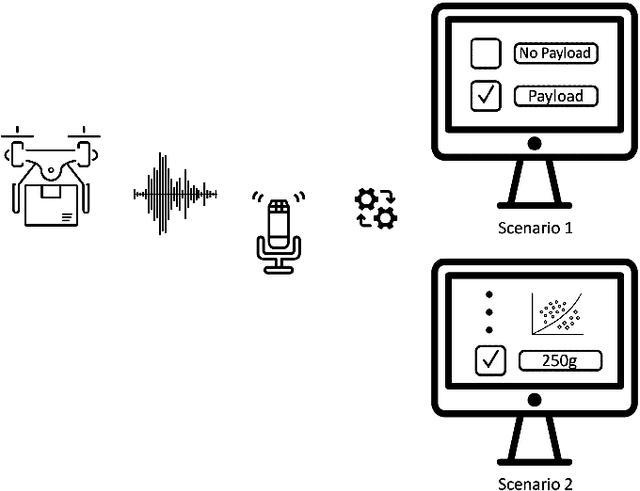



Abstract:The increasing popularity of autonomous and remotely-piloted drones have paved the way for several use-cases, e.g., merchandise delivery and surveillance. In many scenarios, estimating with zero-touch the weight of the payload carried by a drone before its physical approach could be attractive, e.g., to provide an early tampering detection. In this paper, we investigate the possibility to remotely detect the weight of the payload carried by a commercial drone by analyzing its acoustic fingerprint. We characterize the difference in the thrust needed by the drone to carry different payloads, resulting in significant variations of the related acoustic fingerprint. We applied the above findings to different use-cases, characterized by different computational capabilities of the detection system. Results are striking: using the Mel-Frequency Cepstral Coefficients (MFCC) components of the audio signal and different Support Vector Machine (SVM) classifiers, we achieved a minimum classification accuracy of 98% in the detection of the specific payload class carried by the drone, using an acquisition time of 0.25 s---performances improve when using longer time acquisitions. All the data used for our analysis have been released as open-source, to enable the community to validate our findings and use such data as a ready-to-use basis for further investigations.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge