Ahmed Hussain
Near Field Tapering with Slepian Window: Balancing the Range Angle Sidelobe Trade off
Nov 16, 2025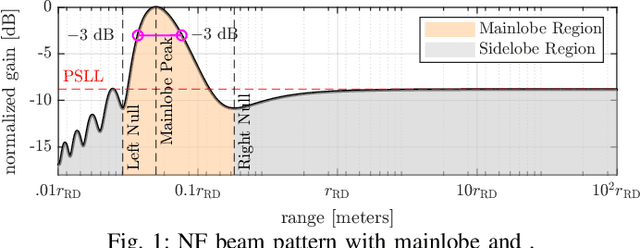
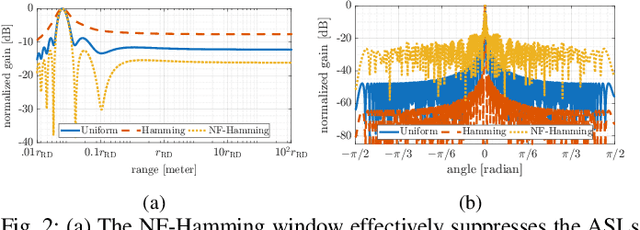
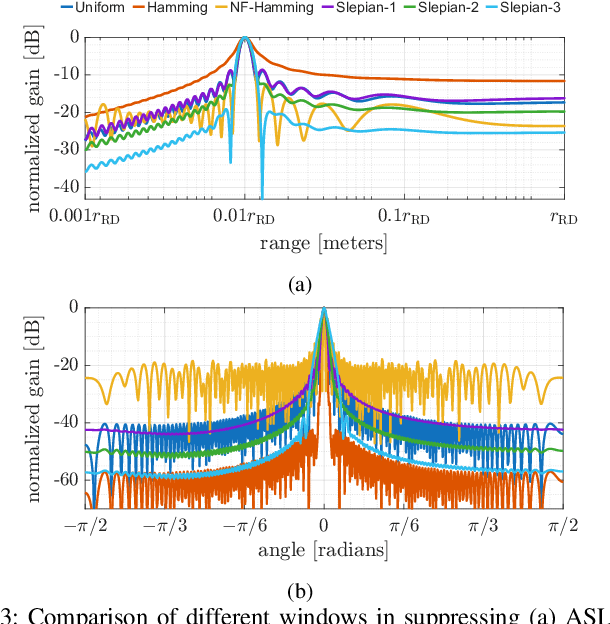
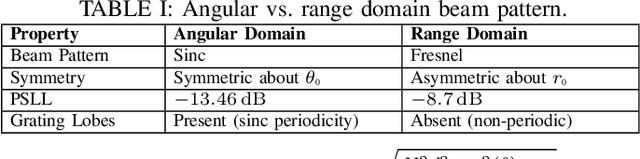
Abstract:Near-field beamforming enables target discrimination in both range (axial) and angle (lateral) dimensions. Elevated sidelobes along either dimension, however, increase susceptibility to interference and degrade detection performance. Conventional amplitude tapering techniques, designed for far-field scenarios, cannot simultaneously suppress axial and lateral sidelobes in near-field. In this letter, we propose a Slepian-based amplitude tapering approach that maximizes mainlobe energy concentration, achieving significant sidelobe reduction in both dimensions. Numerical results show that the proposed taper improves peak sidelobe suppression by approximately 24 dB in the lateral domain and 10 dB in the axial domain compared to a conventional uniform window.
Uniform Circular Arrays in Near-Field: Omnidirectional Coverage with Limited Capacity
Nov 16, 2025Abstract:Recent studies suggest that uniform circular arrays (UCAs) can extend the angular coverage of the radiative near field region. This work investigates whether such enhanced angular coverage translates into improved spatial multiplexing performance when compared to uniform linear arrays (ULAs). To more accurately delineate the effective near field region, we introduce the effective beamfocusing Rayleigh distance (EBRD), an angle dependent metric that bounds the spatial region where beamfocusing remains effective. Closed form expressions for both beamdepth and EBRD are derived for UCAs. Our analysis shows that, under a fixed antenna element count, ULAs achieve narrower beamdepth and a longer EBRD than UCAs. Conversely, under a fixed aperture length, UCAs provide slightly narrower beamdepth and a marginally longer EBRD. Simulation results further confirm that ULAs achieve higher sum rate under the fixed element constraint, while UCAs offer marginal performance gain under the fixed aperture constraint.
Jailbreaking Large Language Models Through Content Concretization
Sep 16, 2025Abstract:Large Language Models (LLMs) are increasingly deployed for task automation and content generation, yet their safety mechanisms remain vulnerable to circumvention through different jailbreaking techniques. In this paper, we introduce \textit{Content Concretization} (CC), a novel jailbreaking technique that iteratively transforms abstract malicious requests into concrete, executable implementations. CC is a two-stage process: first, generating initial LLM responses using lower-tier, less constrained safety filters models, then refining them through higher-tier models that process both the preliminary output and original prompt. We evaluate our technique using 350 cybersecurity-specific prompts, demonstrating substantial improvements in jailbreak Success Rates (SRs), increasing from 7\% (no refinements) to 62\% after three refinement iterations, while maintaining a cost of 7.5\textcent~per prompt. Comparative A/B testing across nine different LLM evaluators confirms that outputs from additional refinement steps are consistently rated as more malicious and technically superior. Moreover, manual code analysis reveals that generated outputs execute with minimal modification, although optimal deployment typically requires target-specific fine-tuning. With eventual improved harmful code generation, these results highlight critical vulnerabilities in current LLM safety frameworks.
Joint Motion, Angle, and Range Estimation in Near-Field under Array Calibration Imperfections
Jul 17, 2025Abstract:Ultra-massive multiple-input multiple-output MIMO (UM-MIMO) leverages large antenna arrays at high frequencies, transitioning communication paradigm into the radiative near-field (NF), where spherical wavefronts enable full-vector estimation of both target location and velocity. However, location and motion parameters become inherently coupled in this regime, making their joint estimation computationally demanding. To overcome this, we propose a novel approach that projects the received two-dimensional space-time signal onto the angle-Doppler domain using a two-dimensional discrete Fourier transform (2D-DFT). Our analysis reveals that the resulting angular spread is centered at the target's true angle, with its width determined by the target's range. Similarly, transverse motion induces a Doppler spread centered at the true radial velocity, with the width of Doppler spread proportional to the transverse velocity. Exploiting these spectral characteristics, we develop a low-complexity algorithm that provides coarse estimates of angle, range, and velocity, which are subsequently refined using one-dimensional multiple signal classification (MUSIC) applied independently to each parameter. The proposed method enables accurate and efficient estimation of NF target motion parameters. Simulation results demonstrate a normalized mean squared error (NMSE) of -40 dB for location and velocity estimates compared to maximum likelihood estimation, while significantly reducing computational complexity.
Analyzing URA Geometry for Enhanced Spatial Multiplexing and Extended Near-Field Coverage
Jun 18, 2025Abstract:With the deployment of large antenna arrays at high frequency bands, future wireless communication systems are likely to operate in the radiative near-field. Unlike far-field beam steering, near-field beams can be focused within a spatial region of finite depth, enabling spatial multiplexing in both the angular and range dimensions. This paper derives the beamdepth for a generalized uniform rectangular array (URA) and investigates how array geometry influences the near-field beamdepth and the limits where near-field beamfocusing is achievable. To characterize the near-field boundary in terms of beamfocusing and spatial multiplexing gains, we define the effective beamfocusing Rayleigh distance (EBRD) for a generalized URA. Our analysis reveals that while a square URA achieves the narrowest beamdepth, the EBRD is maximized for a wide or tall URA. However, despite its narrow beamdepth, a square URA may experience a reduction in multiuser sum rate due to its severely constrained EBRD. Simulation results confirm that a wide or tall URA achieves a sum rate of 3.5 X more than that of a square URA, benefiting from the extended EBRD and improved spatial multiplexing capabilities.
Prompt, Divide, and Conquer: Bypassing Large Language Model Safety Filters via Segmented and Distributed Prompt Processing
Mar 27, 2025Abstract:Large Language Models (LLMs) have transformed task automation and content generation across various domains while incorporating safety filters to prevent misuse. We introduce a novel jailbreaking framework that employs distributed prompt processing combined with iterative refinements to bypass these safety measures, particularly in generating malicious code. Our architecture consists of four key modules: prompt segmentation, parallel processing, response aggregation, and LLM-based jury evaluation. Tested on 500 malicious prompts across 10 cybersecurity categories, the framework achieves a 73.2% Success Rate (SR) in generating malicious code. Notably, our comparative analysis reveals that traditional single-LLM judge evaluation overestimates SRs (93.8%) compared to our LLM jury system (73.2%), with manual verification confirming that single-judge assessments often accept incomplete implementations. Moreover, we demonstrate that our distributed architecture improves SRs by 12% over the non-distributed approach in an ablation study, highlighting both the effectiveness of distributed prompt processing and the importance of robust evaluation methodologies in assessing jailbreak attempts.
Near-Field Beam Prediction Using Far-Field Codebooks in Ultra-Massive MIMO Systems
Mar 18, 2025Abstract:Ultra-massive multiple-input multiple-output (UM-MIMO) technology is a key enabler for 6G networks, offering exceptional high data rates in millimeter-wave (mmWave) and Terahertz (THz) frequency bands. The deployment of large antenna arrays at high frequencies transitions wireless communication into the radiative near-field, where precise beam alignment becomes essential for accurate channel estimation. Unlike far-field systems, which rely on angular domain only, near-field necessitates beam search across both angle and distance dimensions, leading to substantially higher training overhead. To address this challenge, we propose a discrete Fourier transform (DFT) based beam alignment to mitigate the training overhead. We highlight that the reduced path loss at shorter distances can compensate for the beamforming losses typically associated with using far-field codebooks in near-field scenarios. Additionally, far-field beamforming in the near-field exhibits angular spread, with its width determined by the user's range and angle. Leveraging this relationship, we develop a correlation interferometry (CI) algorithm, termed CI-DFT, to efficiently estimate user angle and range parameters. Simulation results demonstrate that the proposed scheme achieves performance close to exhaustive search in terms of achievable rate while significantly reducing the training overhead by 87.5%.
Near-Field ISAC: Synergy of Dual-Purpose Codebooks and Space-Time Adaptive Processing
Jan 15, 2025



Abstract:Integrated sensing and communication (ISAC) has emerged as a transformative paradigm, enabling situationally aware and perceptive next-generation wireless networks through the co-design of shared network resources. With the adoption of millimeter-wave (mmWave) and terahertz (THz) frequency bands, ultra-massive MIMO (UM-MIMO) systems and holographic surfaces unlock the potential of near-field (NF) propagation, characterized by spherical wavefronts that facilitate beam manipulation in both angular and range domains. This paper presents a unified approach to near-field beam-training and sensing, introducing a dual-purpose codebook design that employs discrete Fourier transform (DFT)-based codebooks for coarse estimation of sensing parameters and polar codebooks for parameter refinement. Leveraging these range and angle estimates, a customized low-complexity space-time adaptive processing (STAP) technique is proposed for NF-ISAC to detect slow-moving targets and efficiently mitigate clutter. The interplay between codebooks and NF-STAP framework offers three key advantages: reduced communication beam training overhead, improved estimation accuracy, and minimal STAP computational complexity. Simulation results show that the proposed framework can reduce STAP complexity by three orders of magnitude, validating efficacy, and highlighting the potential of the proposed approach to seamlessly integrate NF communication and sensing functionalities in future wireless networks.
Challenges of Radio Frequency Fingerprinting: From Data Collection to Deployment
Oct 25, 2023Abstract:Radio Frequency Fingerprinting (RFF) techniques promise to authenticate wireless devices at the physical layer based on inherent hardware imperfections introduced during manufacturing. Such RF transmitter imperfections are reflected into over-the-air signals, allowing receivers to accurately identify the RF transmitting source. Recent advances in Machine Learning, particularly in Deep Learning (DL), have improved the ability of RFF systems to extract and learn complex features that make up the device-specific fingerprint. However, integrating DL techniques with RFF and operating the system in real-world scenarios presents numerous challenges. This article identifies and analyzes these challenges while considering the three reference phases of any DL-based RFF system: (i) data collection and preprocessing, (ii) training, and finally, (iii) deployment. Our investigation points out the current open problems that prevent real deployment of RFF while discussing promising future directions, thus paving the way for further research in the area.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge