Ahmad Taha
A Survey on Semantic Communication for Vision: Categories, Frameworks, Enabling Techniques, and Applications
Jan 29, 2026Abstract:Semantic communication (SemCom) emerges as a transformative paradigm for traffic-intensive visual data transmission, shifting focus from raw data to meaningful content transmission and relieving the increasing pressure on communication resources. However, to achieve SemCom, challenges are faced in accurate semantic quantization for visual data, robust semantic extraction and reconstruction under diverse tasks and goals, transceiver coordination with effective knowledge utilization, and adaptation to unpredictable wireless communication environments. In this paper, we present a systematic review of SemCom for visual data transmission (SemCom-Vision), wherein an interdisciplinary analysis integrating computer vision (CV) and communication engineering is conducted to provide comprehensive guidelines for the machine learning (ML)-empowered SemCom-Vision design. Specifically, this survey first elucidates the basics and key concepts of SemCom. Then, we introduce a novel classification perspective to categorize existing SemCom-Vision approaches as semantic preservation communication (SPC), semantic expansion communication (SEC), and semantic refinement communication (SRC) based on communication goals interpreted through semantic quantization schemes. Moreover, this survey articulates the ML-based encoder-decoder models and training algorithms for each SemCom-Vision category, followed by knowledge structure and utilization strategies. Finally, we discuss potential SemCom-Vision applications.
Enhancing Network Security Management in Water Systems using FM-based Attack Attribution
Mar 03, 2025


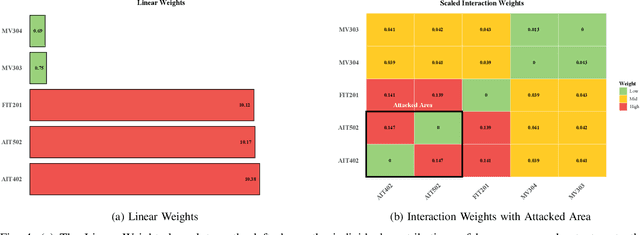
Abstract:Water systems are vital components of modern infrastructure, yet they are increasingly susceptible to sophisticated cyber attacks with potentially dire consequences on public health and safety. While state-of-the-art machine learning techniques effectively detect anomalies, contemporary model-agnostic attack attribution methods using LIME, SHAP, and LEMNA are deemed impractical for large-scale, interdependent water systems. This is due to the intricate interconnectivity and dynamic interactions that define these complex environments. Such methods primarily emphasize individual feature importance while falling short of addressing the crucial sensor-actuator interactions in water systems, which limits their effectiveness in identifying root cause attacks. To this end, we propose a novel model-agnostic Factorization Machines (FM)-based approach that capitalizes on water system sensor-actuator interactions to provide granular explanations and attributions for cyber attacks. For instance, an anomaly in an actuator pump activity can be attributed to a top root cause attack candidates, a list of water pressure sensors, which is derived from the underlying linear and quadratic effects captured by our approach. We validate our method using two real-world water system specific datasets, SWaT and WADI, demonstrating its superior performance over traditional attribution methods. In multi-feature cyber attack scenarios involving intricate sensor-actuator interactions, our FM-based attack attribution method effectively ranks attack root causes, achieving approximately 20% average improvement over SHAP and LEMNA.
Reconfigurable Intelligent Surface-Assisted Cross-Layer Authentication for Secure and Efficient Vehicular Communications
Mar 15, 2023



Abstract:Intelligent transportation systems increasingly depend on wireless communication, facilitating real-time vehicular communication. In this context, message authentication is crucial for establishing secure and reliable communication. However, security solutions must consider the dynamic nature of vehicular communication links, which fluctuate between line-of-sight (LoS) and non-line-of-sight (NLoS). In this paper, we propose a lightweight cross-layer authentication scheme that employs public-key infrastructure-based authentication for initial legitimacy detection while using keyed-based physical-layer re-authentication for message verification. However, the latter's detection probability (P_d) decreases with the reduction of the signal-to-noise ratio (SNR). Therefore, we examine using Reconfigurable Intelligent Surface (RIS) to enhance the SNR value directed toward the designated vehicle and consequently improve the P_d, especially for NLoS scenarios. We conducted theoretical analysis and practical implementation of the proposed scheme using a 1-bit RIS, consisting of 64 x 64 reflective units. Experimental results show a significant improvement in the P_d, increasing from 0.82 to 0.96 at SNR = - 6 dB for an orthogonal frequency division multiplexing system with 128 subcarriers. We also conducted informal and formal security analyses, using Burrows-Abadi-Needham (BAN)-logic, to prove the scheme's ability to resist passive and active attacks. Finally, the computation and communication comparisons demonstrate the superior performance of the proposed scheme compared to traditional crypto-based methods.
Quickest Change Detection in Statistically Periodic Processes with Unknown Post-Change Distribution
Mar 06, 2023Abstract:Algorithms are developed for the quickest detection of a change in statistically periodic processes. These are processes in which the statistical properties are nonstationary but repeat after a fixed time interval. It is assumed that the pre-change law is known to the decision maker but the post-change law is unknown. In this framework, three families of problems are studied: robust quickest change detection, joint quickest change detection and classification, and multislot quickest change detection. In the multislot problem, the exact slot within a period where a change may occur is unknown. Algorithms are proposed for each problem, and either exact optimality or asymptotic optimal in the low false alarm regime is proved for each of them. The developed algorithms are then used for anomaly detection in traffic data and arrhythmia detection and identification in electrocardiogram (ECG) data. The effectiveness of the algorithms is also demonstrated on simulated data.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge