Zexin Fang
The Price of Ignorance: Information-Free Quotation for Data Retention in Machine Unlearning
Apr 13, 2026Abstract:When users exercise data deletion rights under the General Data Protection Regulation (GDPR) and similar regulations, mobile network operators face a tradeoff: excessive machine unlearning degrades model accuracy and incurs retraining costs, yet existing pricing mechanisms for data retention require the server to know every user's private privacy and accuracy preferences, which is infeasible under the very regulations that motivate unlearning. We ask: what is the welfare cost of operating without this private information? We design an information-free ascending quotation mechanism where the server broadcasts progressively higher prices and users self-select their data supply, requiring no knowledge of users' parameters. Under complete information, the protocol admits a unique subgame-perfect Nash equilibrium characterized by single-period selling. We formalize the Price of Ignorance -- the welfare gap between optimal personalized pricing (which knows everything) and our information-free quotation (which knows nothing) -- and prove a three-regime efficiency ordering. Numerical evaluation across seven mechanisms and 5000 Monte Carlo runs shows that this price is near zero: the information-free mechanism achieves >=99% of the welfare of its information-intensive benchmarks, while providing noise-robust guarantees and comparable fairness.
Balancing Functionality and GDPR-Driven Privacy in ISAC Trajectory Sharing
Apr 09, 2026Abstract:Integrated Sensing and Communications (ISAC) enables trajectory sharing that enhances beamforming, resource allocation, and cooperative perception, yet raises fundamental privacy concerns under the General Data Protection Regulation (GDPR) data minimisation principle. This paper proposes a Fisher Information Density (FID)-constrained trajectory sharing framework that enforces a local lower bound on estimation uncertainty, providing hard, quantifiable privacy guarantees by construction. Unlike fixed-noise approaches, the proposed method bounds the Privacy Leak Ratio (PLR) regardless of sensing power or adversarial post-processing, ensuring that no trajectory segment can be reconstructed beyond a prescribed accuracy threshold. Simulations on the OpenTraj dataset demonstrate that the framework keeps the average PLR below 20-25% and the maximum leakage segment duration under 2-2.5 s, while preserving data utility for downstream tasks such as movement prediction. The resulting criterion is interpretable, model-agnostic, and compatible with GDPR-compliant ISAC system design.
Quality-Aware Denoising of Ultra-Short TDoA Measurements for 5G-NR UAV Localization
Apr 09, 2026Abstract:Reliable positioning is essential for Uncrewed Aerial Vehicles (UAVs) in safety-critical urban operations, yet achieving sub-meter accuracy under stringent latency constraints remains challenging. While 3rd Generation Partnership Project (3GPP) specifies repeated Positioning Reference Signals (PRS) transmissions for accurate Time Difference of Arrival (TDoA) measurements, denoising techniques specifically tailored for extremely limited measurement sequences within 3GPP frameworks remain underexplored. We propose Adaptive Gain Exponential Smoother (AGES), a lightweight filter combining exponentially weighted averaging with adaptive gains informed by 3GPP measurement quality reports. Simulations demonstrate AGES achieves 30-40% reduction in positioning error with only 3-5 repeated measurements while maintaining Fifth Generation New Radio (5G-NR) infrastructure compatibility.
Lightweight Node Selection in Hexagonal Grid Topology for TDoA-Based UAV Localization
Jun 17, 2025Abstract:This paper investigates the optimization problem for TDoA-based UAV localization in low-altitude urban environments with hexagonal grid node deployment. We derive a lightweight optimized node selection strategy based on only RSSI measurements, to pre-select optimal nodes, avoiding extensive TDoA measurements in energy-constrained UAV scenarios. Theoretical and simulation results demonstrate that dynamically selecting the number of reference nodes improves localization performance while minimizing resource overhead.
How Cyclic Acoustic Patterns Influence ASMR Perception: A Signal Processing Perspective
Apr 02, 2025



Abstract:Autonomous Sensory Meridian Response (ASMR) has been remarkably popular in the recent decade. While its effect has been validated through behavioral studies and neuro-physiological measurements such as electroencephalography (EEG) and related bio-signal analyses, its development and triggers remain a subject of debate. Previous studies suggest that its triggers are highly linked with cyclic patterns: predictable patterns introduce relaxation while variations maintain intrigue. To validate this and further understand the impact of acoustic features on ASMR effects, we designed three distinct cyclic patterns with monophonic and stereophonic variations, while controlling their predictability and randomness, and collected ASMR triggering scores through online surveys. Then, we extracted cyclic features and carried out regression analysis, seeking an explainable mapping of cyclic features and ASMR triggers. We found that relaxing effects accumulate progressively and are independent of spatial orientation. Cyclic patterns significantly influence psychological and physical effects, which remain invariant with time. Regression analysis revealed that smoothly spread and energy-dense cyclic patterns most effectively trigger ASMR responses.
Privacy Protection Framework against Unauthorized Sensing in the 5.8 GHz ISM Band
Nov 08, 2024Abstract:Unauthorized sensing activities pose an increasing threat to individual privacy, particularly in the industrial, scientific, and medical (ISM) band where regulatory frameworks remain limited. This paper presents a novel signal process methodology to monitor and counter unauthorized sensing activities. Specifically, we model the pedestrian trajectories as a random process. Then, we leverage the Cram\'er-Rao bound (CRB) to evaluate sensing performance and model it as sampling error of such a random process. Through simulation, we verify the accuracy of monitoring unauthorized sensing activities in urban scenarios, and validate the effectiveness of corresponding mitigation strategies.
A Robust UAV-Based Approach for Power-Modulated Jammer Localization Using DoA
May 15, 2024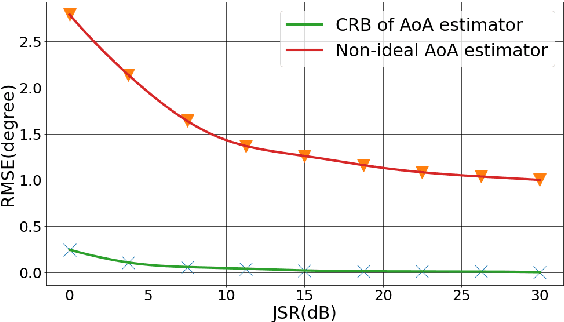
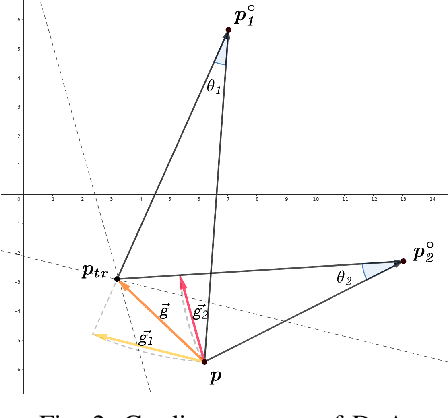
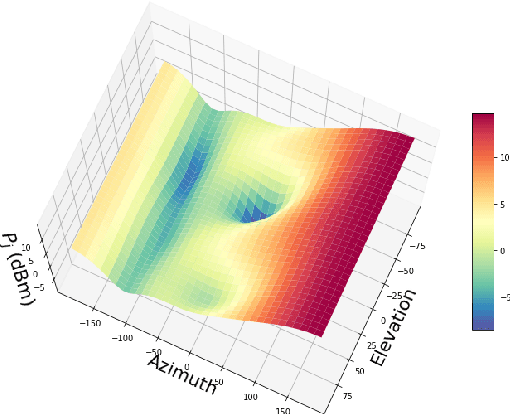
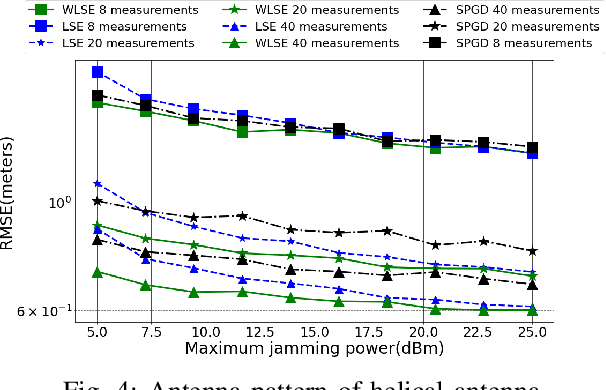
Abstract:Unmanned aerial vehicles (UAVs) are well-suited to localize jammers, particularly when jammers are at non-terrestrial locations, where conventional detection methods face challenges. In this work we propose a novel localization method, sample pruning gradient descend (SPGD), which offers robust performance against multiple power-modulated jammers with low computational complexity.
Robust Federated Learning for Wireless Networks: A Demonstration with Channel Estimation
Apr 03, 2024



Abstract:Federated learning (FL) offers a privacy-preserving collaborative approach for training models in wireless networks, with channel estimation emerging as a promising application. Despite extensive studies on FL-empowered channel estimation, the security concerns associated with FL require meticulous attention. In a scenario where small base stations (SBSs) serve as local models trained on cached data, and a macro base station (MBS) functions as the global model setting, an attacker can exploit the vulnerability of FL, launching attacks with various adversarial attacks or deployment tactics. In this paper, we analyze such vulnerabilities, corresponding solutions were brought forth, and validated through simulation.
3D Cooperative Localization in UAV Systems: CRLB Analysis and Security Solutions
Feb 15, 2024Abstract:This paper presents a robust and secure framework for achieving accurate and reliable cooperative localization in multiple unmanned aerial vehicle (UAV) systems. The Cramer-Rao low bound (CRLB) for the three-dimensional (3D) cooperative localization network is derived, with particular attention given to the non-uniform spatial distribution of anchor nodes. Challenges of mobility and security threats are addressed, corresponding solutions are brought forth and numerically assessed . The proposed solution incorporates two key components: the Mobility Adaptive Gradient Descent (MAGD) and Time-evolving Anomaly Detection (TAD). The MAGD adapts the gradient descent algorithm to handle the configuration changes in cooperative localization systems, ensuring accurate localization in dynamic scenarios. The TAD cooperates with reputation propagation (RP) scheme to detect and mitigate potential attacks by identifying malicious data, enhancing the security and resilience of the cooperative localization.
A Reliable and Resilient Framework for Multi-UAV Mutual Localization
Sep 08, 2023
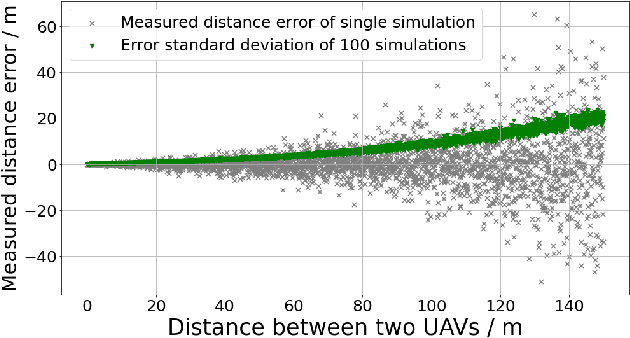


Abstract:This paper presents a robust and secure framework for achieving accurate and reliable mutual localization in multiple unmanned aerial vehicle (UAV) systems. Challenges of accurate localization and security threats are addressed and corresponding solutions are brought forth and accessed in our paper with numerical simulations. The proposed solution incorporates two key components: the Mobility Adaptive Gradient Descent (MAGD) and Time-evolving Anomaly Detectio (TAD). The MAGD adapts the gradient descent algorithm to handle the configuration changes in the mutual localization system, ensuring accurate localization in dynamic scenarios. The TAD cooperates with reputation propagation (RP) scheme to detect and mitigate potential attacks by identifying UAVs with malicious data, enhancing the security and resilience of the mutual localization
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge