Bruno Martin
Exchanging Keys with Authentication and Identity Protection for Secure Voice Communication without Side-channel
Nov 14, 2022


Abstract:Motivated by an increasing need for privacy-preserving voice communications, we investigate here the original idea of sending encrypted data and speech in the form of pseudo-speech signals in the audio domain. Being less constrained than military ``Crypto Phones'' and allowing genuine public evaluation, this approach is quite promising for public unsecured voice communication infrastructures, such as 3G cellular network and VoIP.A cornerstone of secure voice communications is the authenticated exchange of cryptographic keys with sole resource the voice channel, and neither Public Key Infrastructure (PKI) nor Certificate Authority (CA). In this paper, we detail our new robust double authentication mechanism based on signatures and Short Authentication Strings (SAS) ensuring strong authentication between the users while mitigating errors caused by unreliable voice channels and also identity protection against passive eavesdroppers. As symbolic model, our protocol has been formally proof-checked for security and fully validated by Tamarin Prover.
Performance and limitations of dual-comb based ranging systems
Feb 11, 2022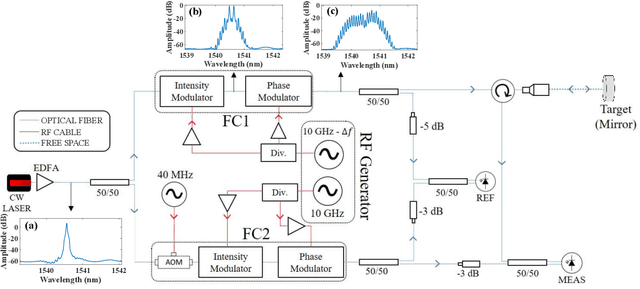


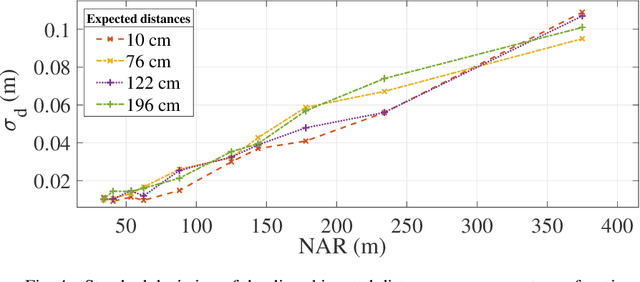
Abstract:Dual-comb LiDARs have the potential to perform high-resolution ranging at high speed. Here, through an implementation involving electro-optic modulators and heterodyne detection, we quantify the ranging systems trade-off between precision and non-ambiguity range (NAR) using a unique performance factor. We highlight the influence of the comb amplitude envelope on the precision with a distance measurement limited by the repetition rate of the optical comb. The influence of the combs repetition rate on the NAR and on the precision is illustrated through a setup allowing distance measurement with a tunable NAR. Finally, we demonstrate the impossibility to resolve different targets, quantify the impact on the measured distance and develop on the conditions in which non-linear effects of the interference make the measurement impossible.
* The authors acknowledge financial support by the Qombs Project (FET Flagship on Quantum Technologies grant No 820419) Quantum simulation and entanglement engineering in quantum cascade laser frequency combs
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge