Var-CNN and DynaFlow: Improved Attacks and Defenses for Website Fingerprinting
Paper and Code
Feb 28, 2018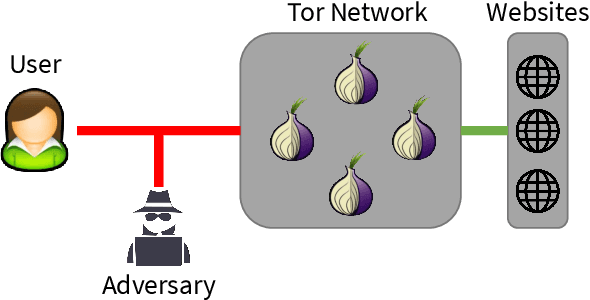
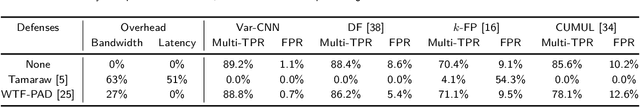
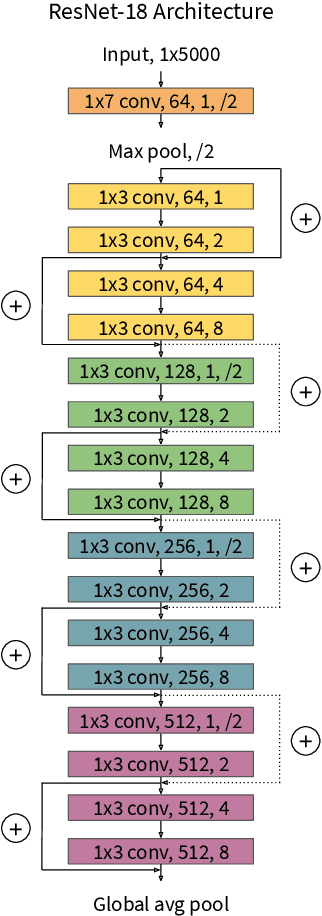

In recent years, there have been many works that use website fingerprinting techniques to enable a local adversary to determine which website a Tor user is visiting. However, most of these works rely on manually extracted features, and thus are fragile: a small change in the protocol or a simple defense often renders these attacks useless. In this work, we leverage deep learning techniques to create a more robust attack that does not require any manually extracted features. Specifically, we propose Var-CNN, an attack that uses model variations on convolutional neural networks with both the packet sequence and packet timing data. In open-world settings, Var-CNN attains higher true positive rate and lower false positive rate than any prior work at 90.9% and 0.3%, respectively. Moreover, these improvements are observed even with low amounts of training data, where deep learning techniques often suffer. Given the severity of our attacks, we also introduce a new countermeasure, DynaFlow, based on dynamically adjusting flows to protect against website fingerprinting attacks. DynaFlow provides a similar level of security as current state-of-the-art and defeats all attacks, including our own, while being over 40% more efficient than existing defenses. Moreover, unlike many prior defenses, DynaFlow can protect dynamically generated websites as well.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge